Enterprise network access in hybrid work
The post-COVID world has changed how, where and when employees work. Technology infrastructure to support popular hybrid work arrangements has advanced exponentially, but this freedom has also introduced new risks for enterprise network security.
With the rise of BYOD (bring your own device), mobility, cloud, and collaboration, security teams are working harder to solve access control security issues than ever before.
Zero Trust is a security model that takes the guesswork out of understanding who or what is trying to access an enterprise network. The model offers a distinct philosophy: never trust, always verify.
“The main principle is providing just in time, just enough access — whether it’s an application requiring access to an API or a user accessing corporate resources,”
says Arjun De, Outcomex Head of Solution Sales.
“How that is implemented, and with what tools, technologies and platforms is going to differ.”

Trust me, I’m your employee… or am I?
“One of the key security challenges for IT teams managing remote workforces is enforcing the same security policies as if the employee was on premise,”
Arjun says.
“Before remote work went mainstream, you’d give them a VPN to access and let your on prem security tools take care of it.”
Those traditional security measures that are location-based and rely on VPN technology – are no longer viable in this multi connected world. Conventionally, any access requests from inside your corporate enterprise network could be trusted – but this is a thing of the past. Today, internal access requests can come from a multitude of places including employees, contractors, vendors, personal and mobile devices, the cloud and IoT.
This can cause headaches for enterprise security teams who need to safeguard against malware and cyber security attacks. They need to know if users are who they say they are, if their devices are secure, and whether certain applications should be talking to one another.
Cisco Zero Trust: comprehensive protection across three distinct fronts
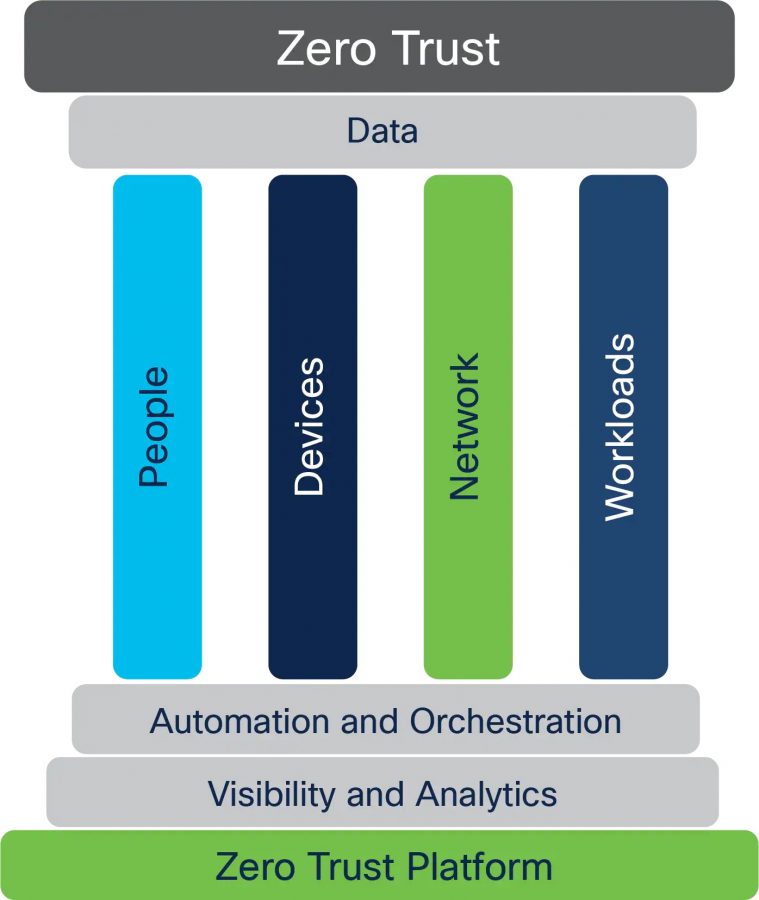
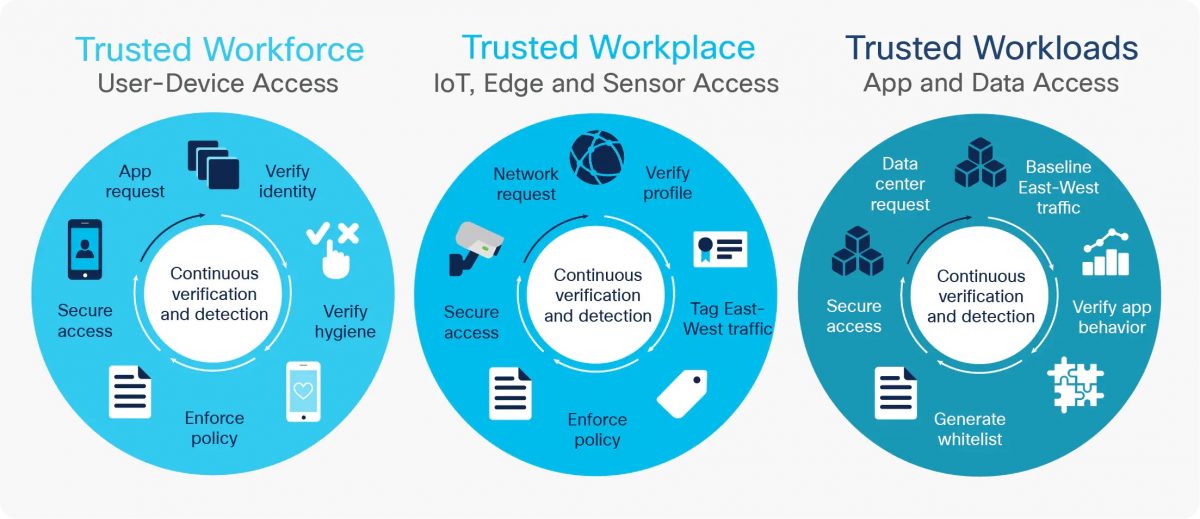
Zero Trust for Workforce
Establishes trust of people and devices, regardless of their location. Limits network access to the right people via secure devices.
Zero Trust for Workloads
Secure access for applications in the cloud, data centres and other virtual environments. Includes secure connections for APIs, microservices and containers that access enterprise applications.
Zero Trust for the Workplace
Access control for all devices that connect to enterprise networks — includes physical and virtual servers, Internet of Things (IoT) and user endpoints like printers and cameras.
Simple and seamless security
Cisco’s Zero Trust solution strikes an important balance between security and usability. Security teams can confidently reduce their organisation’s cyber-attack surface, while users receive a consistent and simple security experience. It’s a win-win for security and productivity.
Tools to make it work
Checking once is not enough in a Zero Trust environment. Once access to the network is granted, Cisco Zero Trust continuously verifies trust.
“Cisco Duo is at the forefront of that — providing the MFA solution that authenticates access to your network, and then gives them just enough access inside,”
Arjun says.
After a user accesses the network, workloads are protected with Cisco Secure Workload allowing application flow visibility and consistent enforcement of security policies. Appropriate network segmentation using identity-based access is provided in the campus environment by Cisco SD-Access.

Forrester recognises Cisco as Zero Trust market leader
Forrester recognised Cisco as a market leader in Forrester’s Zero Trust eXtended Ecosystem Platform Providers report. Cisco received the highest scores possible in The Forrester Wave™ report in the criteria of market approach, ZTX advocacy and ZTX vision and strategy.
Cisco was also among the highest scores in the device security and the future state of Zero Trust infrastructure criteria.
Ready to introduce Zero Trust to your organisation?
Outcomex works with Cisco to provide Zero Trust solutions that ensure only the right people, applications and devices access your network.




