This article has been prepared with a guest author. We hear from Andrew Kay, APJ Director of Systems Engineering at Illumio about how a Zero-Trust approach to ransomware defence can improve security posture.
The global cybersecurity market is set to grow to USD $345.4 billion by 2026. Why the rapid rise? The exponential growth of ransomware and cyberattacks. Users are targets for entry, but attackers are after your critical systems, not laptops and some web servers.
Ransomware delivered in multi-extortion phases, social engineering and insider threat still rank as the most pressing concerns for enterprise/CISOs (Global Cybersecurity Outlook 2022). The ACSC in Australia recently highlighted a 15% increase in reported attacks across businesses of all sizes and in particular critical infrastructure which was echoed by our Five-Eyes colleague across the USA and UK in a recent joint advisory.
Ransomware is still most prevalently delivered through phishing and a user-targeted approach, however application vulnerabilities often have the most widespread opportunity for damage as seen in the recent supply chain attacks which are particularly attractive to attackers.
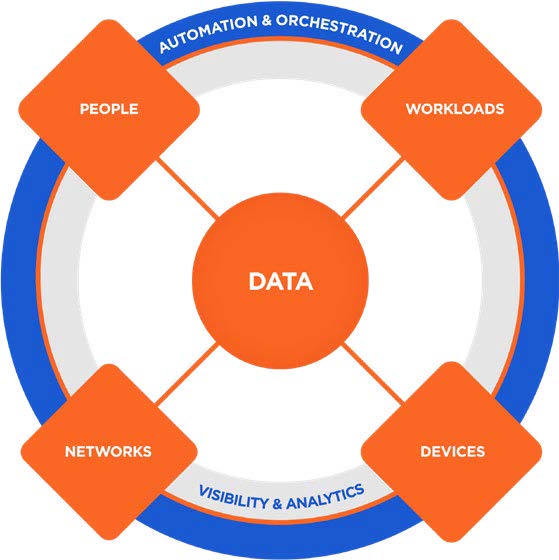
With these concerns, it is understandable that an instinct may be to focus on users. If the human factors provide the most targeted method for successfully gaining a foothold within an enterprise or critical infrastructure organisation, then why wouldn’t we? However, it’s important to not lose sight of the fact that the primary value that runs your business is in the data you hold, the digital service you provide to your consumers, the operational technology that runs manufacturing and distribution plants, and the business processes you are perfecting – not solely in the people and devices they use. Thus, it’s the applications and systems that manage this data and the production line processes that really should be a primary focus for fundamental security controls.
It is, in many cases painfully, apparent that we need to think beyond the annual cyber security training, beyond only limiting the exposure of corporate IT assets to the internet and beyond controlling what individuals can access. Our focus needs to encompass protecting our modern hybrid application hosting environments that, if compromised, would catastrophically affect the business. With increasingly sophisticated threats targeting businesses in every sector, regardless of size, a multi-layered defence and mitigation strategy is key. Taking the largest steps forward first in dissuading a would-be attacker from putting in extra effort will minimise your possibility of making headline news, or weighing up whether they will keep their word if you pay the ransom.
Despite restricting access, you can’t expect everyone to play nice
Imagine you’re hosting a party at home. You take great care in not advertising your location, you’re not listed in any directory services and rather than provide directions to your guests on how to get there you send chauffeured cars to pick everyone up. Only those you know and trust are invited, and you only open the entrance door to the front reception room as they have no business wandering in through the back, through bedroom windows or via the basement that you realise still has the old family silver in an unlocked drawer.
Of course, these are all effective measures in reducing the risk of unwanted guests crashing the party, only allowing entrance in a controlled manner to the space you want guests to be in, and helping prevent anything getting out of hand and damaging the home. However, once they are inside, nothing is stopping them from wandering the entire house via the internal doors when you expect them to only be hobnobbing in the living room.
Replace your home with your IT infrastructure – SDWAN offers a great way to leverage the most effective WAN connection for distributed compute – the internet (allowing for moves away from MPLS connectivity); however, this also opens more possible entry points than you had before meaning it’s possible for ransomware to initiate from and then propagate to more places than ever before.
Secure Access Service Edge (SASE) controls provide easily consumable and bundled security for SDWAN from cloud platforms to allow the minimal number of systems to be securely accessible via the internet. Zero Trust Network Access (ZTNA) and Identity Access Management (IAM) controls overcome limitations of traditional VPNs and ensure only authorised access to the systems individuals need to use; other irrelevant systems are hidden from view. However, once they are on a system, you’re still relying on users to play nice and do the right thing and not utilise the overly permissive connections between the components of the many systems you run, pivoting from those to others, which you assume you’ve hidden from view without much restriction. Enterprise networks, with various forms of convergence (particularly IT and OT in critical infrastructure such as manufacturing, healthcare and energy) are bringing more and more systems within reach, and result in large attack surfaces behind any SASE curtain that’s put up.
Now you may say, hold on a minute, you’ve also employed the services of some bouncers (security personnel) that will spot anyone stepping out of line and will do something about it. But this is a reactive security measure, not dissimilar to AI/ML based endpoint detection and response (EDR) solutions, which often need to see a pattern of bad behaviour before being able to make any judgement calls and needing to be able to react faster than the malicious user is moving. Recent newsworthy breaches continue to show that this alone is also not sufficient as the backstop for “front door protections”.
In many cases, users (susceptible to human nature) are still interacting with datacentre assets, often through VDI/RDP communications, trusted insiders that have existing access to “specific systems”. Often a multitude of apps are used by customers, business partners and public that can’t be secured in a ZTNA fashion, and well-crafted phishing attacks would be able to bypass the investment in IAM controls potentially utilising such methods of hacking MFA.
Zero Trust means just that, and identity extends to workloads
Andrew Kay, Illumio’s Director of Systems Engineering, says that while IAM, SASE and AI EDR are important parts of an enterprise security strategy, a significant risk to ransomware remains even with these capabilities in place. Each of these tools plays an important role in a comprehensive ransomware protection strategy, but none of them are at their best when they work alone. If the most important assets you have are the systems behind the interfaces that users access, perhaps they also shouldn’t be our first port of call in the journey to Zero Trust.
“Ransomware is becoming more indiscriminate; everybody is a target, and we need multi-pronged defences starting with inside-out protection of our critical systems that would be most affected by a ransom event.”
“Rather than relying on limiting your external exposure to the public and to your employees and being prepared to clean up and recover from an attack when it happens, you can get out in front of this,” Andrew says.
Unfortunately, placing our trust in authorised and unauthorised users doing the right thing is really an antithesis of Zero Trust and least privilege concepts. While IAM, SASE and AI-driven EDR focus on user access permissions, limiting your exposure, reacting to threats and forming important pillars of a Zero Trust philosophy; a real key Zero Trust element lies in controlling data availability when someone inevitably breaches your perimeter.
Adding containment and segmentation to the mix
Let’s go back to the house party analogy. What if your guests not only entered via just the reception room, but only had access to this room and the adjacent guest bathroom? If all the internal doors are locked to other parts of the house, the basement is only accessible from a trap door in the study, food is only ever brought out of the kitchen and guests don’t need to put their own plates in the dishwasher, they’re not free to roam, and your property is protected. Containment and segmentation offer the same protection for your IT estate and make sure that you are aware of what should be accessible to which users in the first place.
“Even if you have limited exposure of your networks to the outside world, thousands of servers that sit next to each other on an internal vLAN don’t need to be able to talk to each other. That’s like rolling out the red carpet to hackers who can exploit those connections to move through every part of your system,” says Andrew.
By segmenting your network and controlling how your systems communicate, you can minimise risk, prevent and contain breaches. Utilising containment through segmentation – even as an attack is in progress – provides much-needed defence for your data.
“Take away the endpoints and some web servers you may have disruption and downtime, but that’s not necessarily business-critical. Take the data away or the systems that manage the data, and the business doesn’t run,” Andrew says.
Most organisations have tested the waters with classic 3-tiered datacentre segmentation, however many are now doing it to a degree that will prevent the spread of a determined ransomware attack across modern hybrid environments.
Contain first, provide access second and respond third
Containment and segmentation won’t allow movement between systems through unnecessary channels. Even if you have gained credentials, through takeover, impersonation or simply allocation by being a registered employee or business partner, segmentation will prevent you from going wandering off your allocated path. Containment thwarts the reconnaissance stage of ransomware attacks, it “corners” each attacker so they can’t move freely within your network, and you will benefit from early warning system trip wires for hunters and responders, and accelerate detection and response.
Zero trust segmentation is the only way to ensure that a compromise in any of your application components doesn’t automatically result in a much wider breach.
This is reinforced by advisories, industry regulation and indeed hackers themselves. The joint advisory lists “Limit access to resources over internal networks” as a key mitigation, ASD lists network segmentation as an excellent strategy and “highly effective” at limiting the impact of an intrusion; finance, energy and other critical infrastructure verticals require security architecture with segmentation at its core; and analysts such as Forrester deem it an essential pillar of Zero Trust and Gartner who indicate that identity-based segmentation is a mature, mainstream control and provides transformation benefit within 2 years. Noticeably quicker than SASE that between 2 and 5 years to show its value.
Russian newspaper website Lenta[.]ru recently published an anonymous interview with a threat actor who claims to work with REvil and other sophisticated ransomware collectives who said that one specific, preventive defence works against ransomware – network segmentation.
A blended approach is important for enterprise ransomware protection and placing controls that protect from the inside-out will secure your critical assets

Proactively protect your most important applications, limit workload exposure through identity-based segmentation
Secure the distributed and remote workforce and Control user access
Have a playbook to react to ransomware – Quickly and dynamically block network communication in an application, environment, location or the entire global network to freeze propagation of ransomware as well as EDR, backup and incident response recovery plans
Whether you like C(ontainment)-EDR or ED-C(ontainment)-R as a place for where containment and segmentation comes in your protection strategy, it’s a vital component in the protection against ransomware and when done with modern solutions is not hard and doesn’t impact your environment, and will enable you to continue to host many more successful house parties.
Segment in minutes with Illumio Core
Illumio Core assigns an identity to each system in your data centres or cloud environments, simplifying network segmentation and internal connectivity controls. The containment and segmentation solution provides intelligent visibility, simple policy creation, and automated segmentation and enforcement to stop attacks, that will inevitably land, from spreading.
Partnering with Illumio and Outcomex
Illumio, the pioneer and market leader of Zero Trust segmentation, prevents breaches from becoming cyber disasters. Ask Outcomex about Illumio and how we can support you with ransomware mitigation and segmentation solutions that see risk, isolate attacks, and secure data across apps, clouds, data centres, and endpoints.
Segmented or risking your entire network? Let’s talk trust. Partner with Outcomex and Illumio to automate your journey to Zero Trust segmentation.



